I created the Identity Bridge to make it easier for IT admins to set up user access across cloud systems. However, user access is also required across on-premises systems. This is where problems such as cross-forest managers, domain controller line of sight, and, ultimately, on-premises Active Directory consolidation can become costly to address.
This post describes a free and supported way to solve the cross-forest manager problem. In other words, how to synchronize your on-premises AD forests to Azure AD when you have Manager/Employee relationships that span forests. This solution does not require an intermediate forest and uses supported Azure AD Connect functionality. The multi-forest manager problem is a common and long-standing Active Directory limitation that is well-described here on Reddit. The manager attribute is used more and more in the Teams Organization tab and Entra ID Governance workflows. I’ve validated the “Shadow Account Solution” below with experts at Microsoft, identity architects at customers, and a proof of concept in Azure. However, if you see any flaws or areas for improvement, please let me know!
The Intermediate Forest Problem
The cloud is supposed to simplify things. Unfortunately, to get to the cloud, organizations sometimes face complex directory consolidations. An organization that can’t muster the resources to perform a full directory consolidation may create an “intermediate forest” and then sync that consolidated directory to Azure AD. This “intermediate forest” approach creates a host of problems:
- different identities used for network/workstation access vs. O365 access
- broken password writeback & Self-Service Password Reset scenarios
- broken device writeback, Windows Hello for Business, Autopilot scenarios
- broken user and group writeback scenarios from Microsoft (in the future)
We want to avoid intermediate forests in overcoming the Active Directory limitations around cross-forest managers.
The Shadow Account Solution
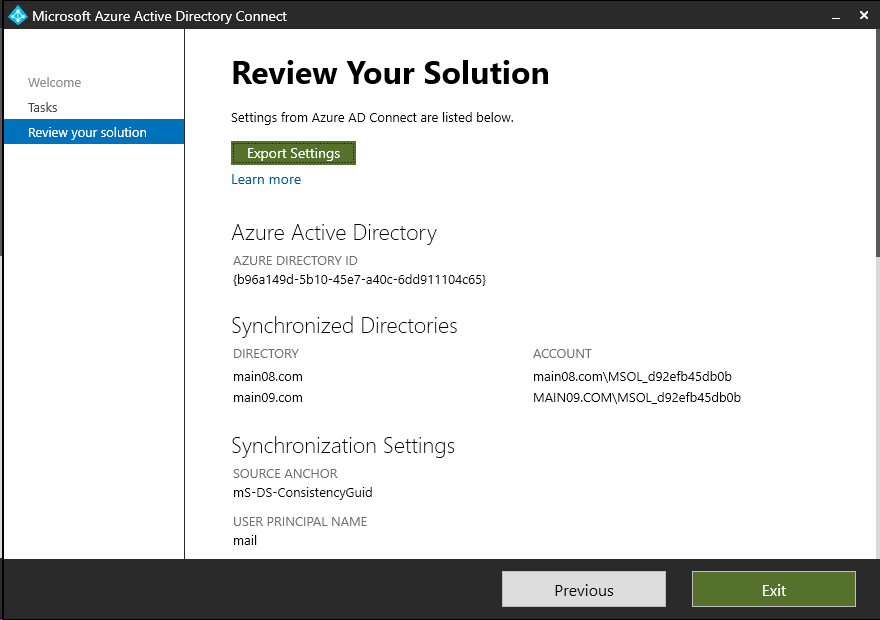
Azure AD Connect supports synchronization from multiple forests and consolidation of duplicate user objects across these forests. Creating “shadow” representations of users in each relevant forest allows Azure AD Connect to sync managers and direct reports from different forests. This article describes Azure AD Connect user consolidation best practices. Here is how to configure Azure AD Connect to perform this consolidation:
- Sync
UserPrincipalNameto Azure AD based on themailattribute in on-premises AD. - Select the “User identities exist across multiple directories.” option and match using the
mailattribute.
- Ensure that Azure AD Connect uses
mS-DS-ConsistencyGuidto uniquely identify and consolidate users with the same email address across forests.
Here is a screenshot of my proof of concept Azure AD Connect configuration:
Preparing the Forests
I created the proof-of-concept with two AD forests (each composed of two virtual machine domain controllers) on two peered Azure virtual networks. I confirmed that Azure AD Connect syncs user: user1@main08.com to Azure AD with manager: manager@main09.com (and no extra users 🙂 ). Here are the users I created in each forest.
Forest: main08.com
- UPN: user1@main08.com
- mail: user1@main08.com
- manager: manager@main08.com
- UPN: manager@main08.com <– “shadow” manager
- mail: manager@main09.com
Forest: main09.com
- UPN: user1@main09.com <– “shadow” user
- mail: user1@main08.com
- UPN: manager@main09.com
- mail: manager@main09.com
How to Prepare the Forests?
Microsoft Identity Manager can keep these shadow accounts up to date from an external source of truth (like an HR system). We are considering adding an on-premises agent to allow the Mindline Identity Bridge to perform this function. Please let me know if this would provide value to your organization!